Cryptographic Testing
Entropy Source Assessment
Consult our experts. We are happy to support you.
What atsec offers:
atsec US offers entropy source assessment specified by the SP800-90 series of documents through its accredited Cryptographic Security Testing (CST) laboratory (NVLAP Lab Code #200658-0). The assessment consists of two parts and will lead to an ESV certificate listing on the NIST website:
- Analysis of the design and operation of the noise source, as well as other aspects of the noise source (conditioning components, health tests, IID assumptions, etc.), need to be documented and reviewed.
- Cryptographic modules that implement an entropy source need to be compliant with Special Publication 800-90B “Recommendation for the Entropy Sources Used for Random Bit Generation”. This involves the statistical testing of raw entropy data (one million samples) collected from a continuous run of the noise source, as well as raw entropy data (another million samples) collected by concatenating 1,000 samples after a restart of the noise source with a total of 1,000 restarts.
Authoritative websites:
More information:
Why our services are important to you:
The CMVP requires that all FIPS 140-3 module validation submissions include documented conformance to SP 800-90B when it is applicable. SP 800-90B, along with corresponding FIPS 140-3 IGs D.J, D.K, and D.O, outline the requirements for an entropy source to be included in a FIPS-approved cryptographic module.
Downloads:
Further information for your certification journey.
The following entropy source implementations are the latest of the 47 that were tested by atsec’s laboratory:
| Vendor / Implementation | Certificate / Date |
|---|---|
| Analog Devices, Inc. TRNG B2 Entropy Source |
E159 2024-07-12 |
| Qualcomm Technologies, Inc. Entropy Source of the Qualcomm(R) Pseudo Random Number Generator (Snapdragon(R) 7 Gen 1) |
E155 2024-07-02 |
| Qualcomm Technologies, Inc. Entropy Source of the Qualcomm(R) Pseudo Random Number Generator (Snapdragon(R) 6 Gen 1) |
E154 2024-07-02 |
| Qualcomm Technologies, Inc. Entropy Source of the Qualcomm(R) Pseudo Random Number Generator |
E153 2024-07-02 |
| Qualcomm Technologies, Inc. Entropy Source of the Qualcomm(R) Pseudo Random Number Generator |
E152 2024-07-02 |
| Oracle Corporation Oracle Linux 9 Kernel CPU Time Jitter RNG Entropy Source |
E151 2024-07-02 |
| IBM Corporation IBM Power10 RNG (with conditioning) |
E150 2024-06-28 |
| Cloudlinux Inc., Tuxcare Division Userspace CPU Time Jitter RNG Entropy Source |
E127 2024-03-04 |
| IBM Corporation IBM Power10 RNG |
E120 2024-02-20 |
| Laird Connectivity Summit CPU Time Jitter RNG Entropy Source |
E119 2024-02-12 |

Still have questions?
Can’t find what you’re looking for? Let’s talk!
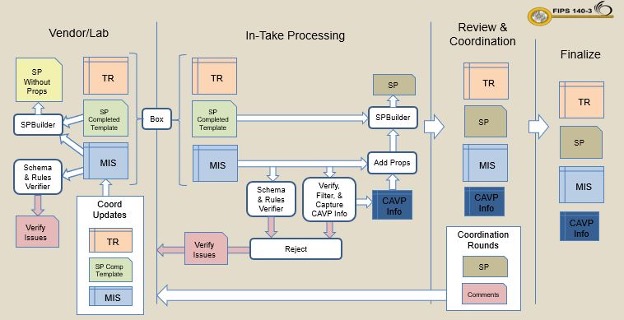
FIPS 140-3 Testing
FIPS 140-3 specifies requirements related to securely designing and implementing cryptographic modules, and compliance is increasingly mandatory worldwide.
Cryptographic Algorithm Testing
Testing that cryptographic algorithms are implemented correctly is a prerequisite for FIPS 140-3 cryptographic module testing and NIAP Common Criteria evaluations.
Common Criteria Evaluation
The Common Criteria (CC), also known as ISO 15408, is an internationally recognized standard used to specify and assess the security of IT products.
The Information Security Provider
Read Our Latest Blog Articles
Learn the latest and greatest about information security. You’ll find insights and analyses of recent developments in technology and policy on our blog.
-
First SP800-140Br1 Compliant FIPS 140-3 Certificates
On July 11th, 2024, the first three FIPS 140-3 certificates for NIST’s SP800-140Br1 pilot program were posted on the NIST website. atsec information security was one of the labs that took part in the pilot program. SP 800-140Br1 specifies modifications of the methods to be used by a…
-

Changes Coming to NIAP Entropy Assessment Reports in 2025
“What do you say to a room full of DRBGs standing around you? Everyone, please be seeded.” -Quin, atsec tester When things change, it can help to approach that change with a light heart like this.Recently, NIAP announced that Entropy Assessment Reports (EARs) must include a NIST Entropy…
-

BSI NESAS CCS-GI Scheme Updates
We’d like to inform our customers and partners that the German Federal Office for Information Security (BSI) recently published new documents approving the use of additional Security Assurance Specifications (SCAS) under the BSI 5G NESAS Certification and Evaluation Scheme (BSI NESAS CCS-GI). We encourage our customers to fully…
