-

atsec at AutoCS 2026: Leveraging CC, FIPS, and PCI for Automotive Cybersecurity
atsec recently attended the 9th AutoCS to help establish a secure future for connected vehicles.
-

atsec’s Experience at the Post-Quantum Cryptography Workshop at the KTH Royal Institute of Technology
The PQC Workshop at the KTH Royal Institute of Technology was a trove of valuable insights.
-

Building the Future: XDRBG’s Standardization as Part of SP800-90A
The algorithm for the XOF-based DRBG has been finished, and atsec is proud to have contributed to the project!
-

CAVP Issues Updated Guidance on Algorithm Certificate Posting
CAVP has made it clear: just include facts in ACVTS data fields.
-

BSI’s Study Analyzing RBG Usage in Browsers
atsec conducted a study for the BSI on the use of RBGs in internet browsers.
-

Digging into some FIPS ‘n’ Chips
atsec’s FIPS ‘n’ Chips crypto module bootcamp wrapped up this week, and it was a blast!
-
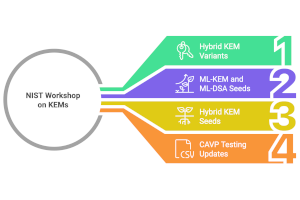
A Glimpse of the Future: NIST’s KEM Workshop
NIST held a workshop on the future of Key Encapsulation Mechanisms (KEMs), featuring several interesting proposals.
-

FIPS ‘n’ Chips Crypto Module Bootcamp
atsec and UT Austin are excited to host the second Crypto Module Bootcamp, free for all participants!
-

Final Call to Submit for Interim Validation
The CMVP is moving back to its normal certification process, which means interim submissions are being closed.
